A health data aggregator app looks simple in a demo. Connect a few APIs, pull patient records, display a dashboard. However, production is a different story.
Aggregating data from EHRs, payer systems, labs, pharmacies, and wearables means confronting fragmented standards, mismatched patient identities, inconsistent data quality, and serious HIPAA obligations. Meanwhile, CMS interoperability rules are pushing the market toward broader data exchange, and ONC reports that certified health IT now supports over 96% of hospitals and 78% of office-based physicians, making interoperable data central to modern care workflows.
But access isn’t usability. Without normalization, identity reconciliation, consent tracking, and reliable data surfacing, aggregation creates noise instead of value. The real challenge isn’t pulling data, it’s building a platform that makes multi-source health information secure, auditable, and clinically useful.
Building a reliable aggregation platform requires careful planning across interoperability, security, and architecture from the start. If you’re evaluating how to approach this, explore our healthcare app development services to see how we design systems for real-world healthcare environments.
What Is a Health Data Aggregator App?
A health data aggregator app is a healthcare application that collects patient or operational health data from multiple sources, standardizes it, and presents it in one usable interface. Those sources can include EHR and EMR systems, payer platforms, lab systems, pharmacies, wearable devices, remote patient monitoring tools, and patient-reported inputs. The goal is not just data access, it is creating a more complete and actionable view of health information across fragmented systems.
This is different from a simple point-to-point integration. A basic integration may move data from one system to another, but a true aggregation app pulls information from several sources, reconciles differences, preserves source context, and makes the data usable for a specific workflow. That workflow might support a patient reviewing their history in one portal, a clinician viewing a longitudinal record, or a care management team monitoring high-risk patients across disconnected platforms.
In practice, health data aggregation apps usually fall into a few categories:
- Patient-facing apps that combine records, medications, appointments, lab results, or wearable data in one place
- Clinician dashboards that provide a unified view of data from multiple care settings
- Care coordination tools that help teams track encounters, treatment plans, and follow-up needs across providers
- Digital health platforms that combine device, behavioral, and clinical data to support ongoing care
- Analytics or population health tools that aggregate data for operational insight, risk analysis, or reporting
The value of aggregation is clear, but the execution is where most teams struggle. Even when multiple systems technically expose APIs, they often structure data differently, update records at different intervals, and identify patients in inconsistent ways. That means a health data aggregator app must do much more than connect endpoints. It must normalize, validate, secure, and contextualize healthcare data so users can actually trust what they see.
5 Core Building Blocks of a Health Data Aggregator App
A successful health data aggregator app depends on more than API connectivity. It needs a solid architecture that can ingest data from multiple healthcare systems, match it to the right patient, normalize it into a usable structure, protect it under HIPAA-aligned controls, and present it clearly enough for users to trust. That is why teams often work with a partner focused on healthcare software development when building products that involve EHR integrations, PHI, and interoperability requirements. If any one of those layers is weak, the entire product becomes harder to scale and riskier to use.
1. Data source connectivity
The first layer is source connectivity. Most modern aggregation products rely on a combination of FHIR APIs, HL7 interfaces, SMART on FHIR authorization flows, and, in some cases, custom integrations for older or proprietary systems. FHIR has made healthcare interoperability far more practical, but implementation still varies across vendors and organizations. That means teams often need to support both standards-based and non-standard integration methods instead of assuming one protocol will cover every use case.
2. Identity and patient matching
Once data starts flowing in, the app has to determine which records belong to the same person. This sounds simple, but patient matching is one of the hardest parts of healthcare data aggregation. Different systems may store variations in names, addresses, dates of birth, phone numbers, or identifiers. Without a careful identity strategy, the app can create fragmented patient views or, worse, combine records that should never have been merged.
3. Data normalization and mapping
Raw healthcare data is rarely consistent across systems. One source may structure medications differently from another. Lab values may use different formats, codes, or timestamps. Some records may be detailed, while others are sparse. A health data aggregator app needs a canonical data model that converts incoming information into a unified structure while preserving source metadata. This is where terminology mapping, reconciliation logic, and source attribution become essential.
4. Security and access control
Because these platforms often handle protected health information, security has to be built into the architecture from the start. That includes OAuth 2.0-based authorization, role-based access controls, encryption in transit and at rest, detailed audit trails, session controls, and vendor-level risk management. HHS makes clear that regulated healthcare systems handling electronic protected health information must implement administrative, physical, and technical safeguards under the HIPAA Security Rule.
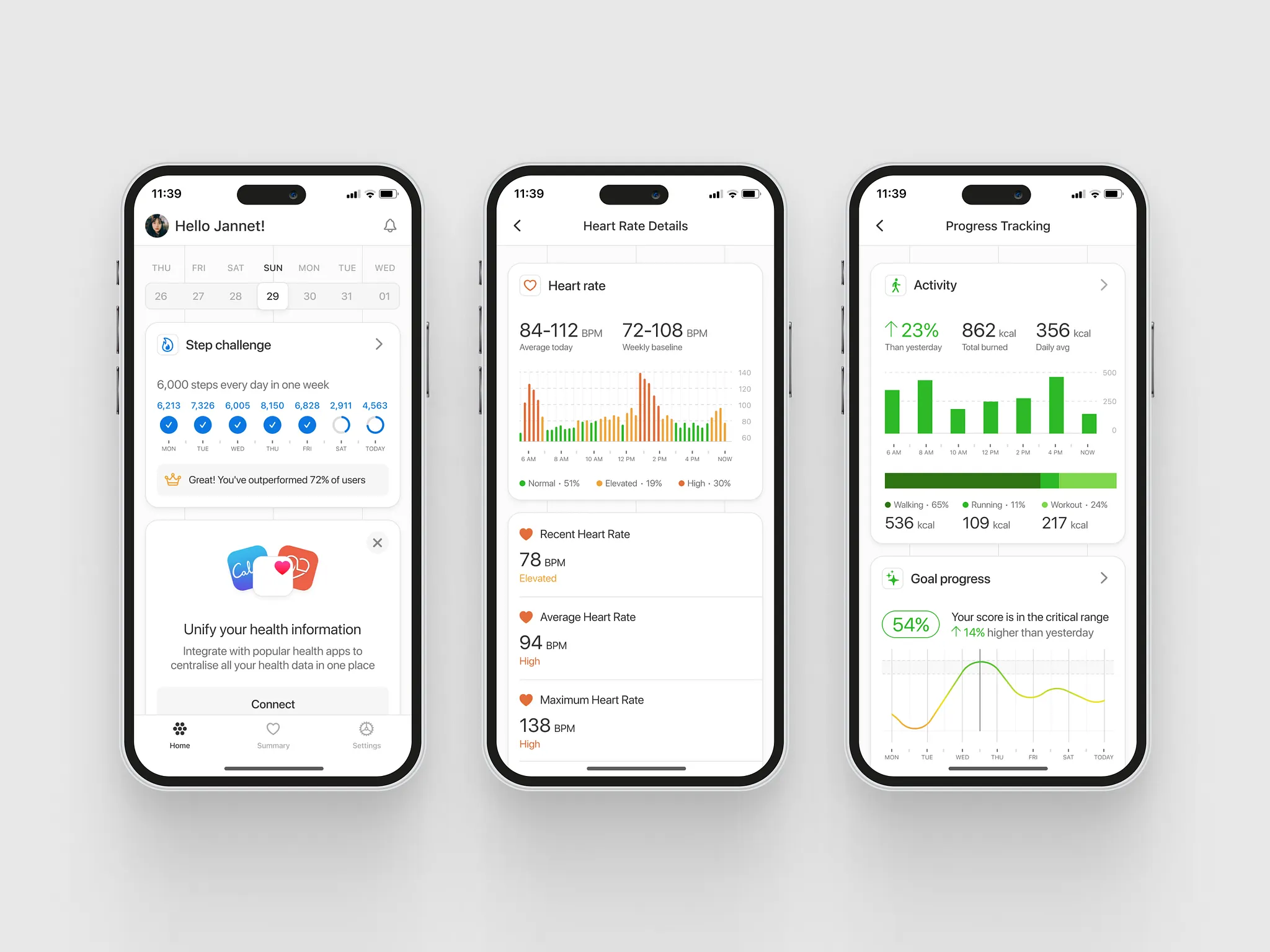
5. Presentation layer and user experience
The final layer is the user-facing experience. Even well-aggregated data loses value if users cannot tell where it came from, how recent it is, or whether parts of the record are incomplete. Strong aggregation apps show source attribution, last-sync timing, and clear organization across encounters, medications, labs, devices, or care plans. In healthcare, user experience is not just about design polish, it is about helping people interpret multi-source data safely and confidently.
The Biggest Challenges in Building a Health Data Aggregator App
Building a health data aggregator app gets difficult the moment real-world healthcare systems enter the picture. On paper, modern APIs and interoperability standards make aggregation sound straightforward. In practice, most teams discover that the hardest problems are not just technical, they are operational, regulatory, and product-related at the same time. That is why many teams study resources like FHIR API integration in healthcare interoperability and how to integrate your healthcare app with Epic EHR before committing to architecture decisions.
Interoperability is uneven across systems
One of the biggest misconceptions in healthcare app development is that FHIR solves interoperability on its own. FHIR has absolutely improved healthcare data exchange, but even strong standards do not guarantee uniform implementation across EHRs, provider groups, payers, labs, and third-party platforms. Different systems may expose different resources, support different workflows, or implement standards with enough variation to create extra development and testing work. ONC’s HTI-1 rule continues advancing interoperability and standards adoption, but product teams still need to plan for real-world inconsistency across endpoints.
Aggregated data can be incomplete, stale, or contradictory
A demo often assumes that every source returns clean, complete, current data. That is rarely true. One source may have a more recent medication list. Another may have encounter history but no lab values. A wearable feed may update in near real time, while a payer or EHR source updates much more slowly. If the product does not preserve timestamps, source attribution, and reconciliation logic, users may see a combined record that looks complete but is actually misleading. In healthcare, that is not just a UX issue. It is a trust issue.
Patient identity resolution is harder than teams expect
A health data aggregator app only works if it can reliably determine which records belong to which patient. That becomes difficult when names are spelled differently, addresses are outdated, phone numbers change, or one system uses a different patient identifier from another. Teams that underestimate identity resolution often end up with fragmented records, duplicate patient views, or risky record merges. This is one of the clearest examples of why healthcare aggregation is not just an integration project. It is also a data governance and product safety problem.
HIPAA and security obligations expand quickly
As soon as your platform stores, transmits, or exposes electronic protected health information, security requirements become much more serious. HHS states that the HIPAA Security Rule establishes national standards to protect ePHI and requires administrative, physical, and technical safeguards to ensure its confidentiality, integrity, and availability. For aggregation products, that means secure authentication, role-based access, audit logs, encryption, session controls, vendor oversight, and incident readiness cannot be late-stage add-ons. They have to be built into the product from day one.
Consent, authorization, and governance become complex fast
Healthcare data aggregation is not only about whether data can be accessed. It is also about whether it should be accessed, under what authorization, for how long, and with what audit trail. Teams need to track what a user consented to, which systems were connected, when access was granted, and how revocation should work if permissions change. Without clear governance, an aggregation app can become difficult to defend from both a compliance and product-risk standpoint.
Performance and reliability problems appear at scale
Even when initial integrations work, scale creates a second wave of problems. APIs may have rate limits. Source systems may go down temporarily. Sync jobs may fail silently. Webhooks may be delayed or missed. If there is no monitoring, retry logic, queueing, and reconciliation layer, the product can slowly drift away from being dependable. That is especially dangerous in healthcare, where users may assume the record they are viewing is complete and current.
Planning a healthcare data platform? Our team can help you architect it securely from day one.
A strong next step for buyers evaluating implementation partners is to review healthcare software development services and see how interoperability, HL7/FHIR integration, and HIPAA-ready architecture are handled together rather than as separate workstreams.
Best Practices for Building a Secure, Scalable Aggregation App
The best health data aggregator apps are not built by trying to connect every possible source on day one. They are built by narrowing the workflow, defining a trustworthy data model, and designing for security, transparency, and operational resilience from the beginning. Because FHIR is an electronic standard for exchanging healthcare information, it provides a strong foundation for modern interoperability, but it still needs to be paired with product decisions that account for inconsistent source behavior and strict ePHI safeguards.
Start with a narrow, high-value use case
The fastest way to create complexity is to aggregate too much too early. A better approach is to begin with one workflow that clearly benefits from multi-source data, such as medications, visit history, lab results, or remote patient monitoring feeds. This keeps the first release focused, reduces integration sprawl, and makes it easier to validate whether the product is actually useful before expanding.
Design around FHIR, but plan for gaps
FHIR should be the default standard where available because it is specifically designed for electronic healthcare information exchange. But product teams should not assume every source will support the same FHIR resources, implementation quality, or authorization pattern. A strong architecture uses standards first, while still planning for fallback logic, source-specific transforms, and phased integration support when real-world systems do not behave consistently.
Build a canonical data model early
One of the most important architectural decisions is how the app will represent aggregated data internally. A canonical data model helps normalize records from different sources into one consistent structure while preserving source details, timestamps, and provenance. Without that layer, every new integration increases downstream inconsistency and makes reconciliation more fragile.
Treat patient matching as a safety-critical function
Identity resolution should never be treated as a background utility. It affects trust, workflow reliability, and patient safety. Teams should define clear matching rules, preserve confidence signals, and create review paths for lower-confidence matches rather than forcing automatic merges. In aggregation products, a cautious identity strategy is usually better than a fast one.
Build HIPAA-ready controls from day one
HHS states that the HIPAA Security Rule requires appropriate administrative, physical, and technical safeguards to protect electronic protected health information, including its confidentiality, integrity, and availability. For a health data aggregator app, that means access control, encryption, audit logging, session security, vendor oversight, and incident response planning should be part of the initial system design, not postponed until launch preparation.
Make transparency part of the user experience
Users need to understand what they are looking at. That means showing where data came from, when it was last updated, whether it is incomplete, and whether conflicting values exist across sources. Transparent UX reduces misinterpretation and makes the product more defensible, especially when data freshness or source quality varies.
Invest in observability and resilience early
Aggregation products depend on external systems, which means they need strong operational visibility. Monitoring, retries, sync status tracking, queueing, alerting, and reconciliation workflows are essential if the app is expected to remain reliable as integrations grow. This aligns well with Technology Rivers’ product development process, which emphasizes planning integrations, data models, scalability, security, and post-launch monitoring as part of the build lifecycle.
In practice, the best results come from combining interoperability standards, HIPAA-ready architecture, and disciplined product scoping, not from chasing maximum connectivity in the first release. For teams building in regulated healthcare environments, that is usually what separates a demoable prototype from a platform users can actually trust.
6 Common Mistakes That Derail Health Data Aggregator Projects
Many health data aggregation projects do not fail because the idea is weak. They fail because teams underestimate how much healthcare complexity sits behind what looks like a straightforward integration roadmap. The most common mistakes usually appear early, long before launch, and they compound as more systems and users are added.
1. Assuming FHIR alone solves interoperability
FHIR is a major improvement for healthcare data exchange, but it is not a shortcut around implementation variance, missing resources, source-specific workflows, or legacy systems. Teams that treat FHIR as a universal fix often discover late in the process that “FHIR-enabled” does not mean “ready for seamless aggregation.” That usually leads to delays, rework, and fragile logic spread across the application.
2. Aggregating too many sources too early
It is tempting to pitch a unified record that connects everything at once: EHRs, labs, pharmacies, payer APIs, devices, and patient-reported data. In practice, this creates a large testing surface, inconsistent data quality, and too many failure points for an early-stage product. The better approach is to start with a defined workflow, prove value, and then expand source coverage in controlled phases.
3. Underestimating identity matching complexity
A product can have working integrations and still fail if patient matching is unreliable. Duplicate records, fragmented histories, and accidental merges undermine trust quickly. Teams that do not define matching confidence, exception handling, and review workflows usually end up with a system that looks complete on the surface but behaves unpredictably underneath.
4. Hiding data quality issues from users
Some teams try to simplify the interface by masking sync delays, source conflicts, or missing data. That can make the product look cleaner in a demo, but it makes it less trustworthy in production. In healthcare, users need context. Showing source attribution, last-updated times, and conflict indicators is often better than presenting a polished but misleading unified view.
5. Treating compliance as a late-stage checklist
HIPAA, access control, auditability, vendor review, and data governance should shape architecture from the beginning. When compliance is treated as something to “add later,” teams often discover that core parts of the system need redesign. That is one reason companies building regulated products often look at healthcare software development services early, rather than waiting until security gaps have already been built into the platform.
6. Failing to design for operations, not just launch
A health data aggregator app is never just a release project. It is an ongoing operational system that depends on external APIs, changing source behavior, monitoring, retries, and support workflows. Teams that only design for launch often struggle once data volumes grow, integrations expand, and users start depending on the product for real decisions.
These mistakes are common, but they are avoidable. The strongest teams treat aggregation as a long-term healthcare platform problem, not just a feature build.

A Practical Build Sequence for Teams Starting from Scratch
A health data aggregator app should not be built as a giant integration program from day one. The smarter path is to move in phases, each one reducing risk around interoperability, security, usability, and long-term maintainability. That approach is especially important in healthcare, where a product can appear technically functional while still failing on data trust, compliance readiness, or workflow value.
Phase 1: Define one workflow worth aggregating
Start with a narrow use case that clearly benefits from multi-source data. That might be a unified medication history, a patient timeline, a remote patient monitoring feed, or a care coordination dashboard. The goal is to answer one question early: what decision or workflow gets better when data from multiple systems is combined? Teams that begin with that level of clarity usually avoid building broad but shallow products.
Phase 2: Select the right source systems, not every source system
Once the use case is defined, choose only the systems required to support that first workflow. This is where teams should evaluate whether each source is best accessed through FHIR, HL7, SMART on FHIR, or a custom integration path. A good reference point here is how to integrate your healthcare app with Epic EHR because it reflects the kind of planning needed before teams start assuming every major system will connect the same way.
Phase 3: Define your canonical data model before scaling integrations
Before you build too many pipelines, decide how your app will represent the data internally. Encounters, medications, observations, labs, documents, and device data all need consistent definitions, timestamps, provenance rules, and normalization logic. This is the point where many teams realize aggregation is not just about APIs. It is about turning inconsistent source data into a reliable product layer.
Phase 4: Design access, auditability, and HIPAA controls into the foundation
Healthcare teams often regret treating security as a review step instead of an architectural decision. By this phase, the product should already have clear role-based access rules, encryption strategy, audit logging, session control, and vendor risk boundaries. A useful companion resource here is how to ensure your healthcare software is HIPAA compliant in 2026, especially for teams validating whether their early architecture can support real-world PHI handling.
Phase 5: Build ingestion and reconciliation before chasing polish
At this stage, the focus should be on reliable ingestion, source attribution, retry handling, sync visibility, and data reconciliation. Users do not just need data to appear. They need to know where it came from, when it was updated, and whether it conflicts with another source. That is why aggregation products succeed when they prioritize trust signals before interface polish.
Phase 6: Validate usability with real data and real exceptions
Only after the first workflow is live should the team assess whether the aggregated experience actually helps users. Can users understand missing data, stale records, or conflicting values? Do they trust the patient view enough to act on it? In healthcare, the answer often depends as much on transparency and workflow design as it does on technical accuracy. That is also where lessons from how UX design in healthcare apps drives better outcomes become especially relevant.
Phase 7: Expand sources and automation in controlled layers
Once the first workflow is stable, then it makes sense to add more systems, more user roles, and more automation. Expansion should be deliberate. Every new source increases product value, but it also increases matching complexity, governance overhead, sync monitoring needs, and failure scenarios. Teams that scale in layers usually end up with stronger operational visibility and fewer surprises.
A practical build sequence like this keeps a health data aggregator app grounded in business value instead of technical ambition alone. It also creates a stronger path to a production-ready platform, one that can grow without losing trust. For a founder-level perspective on building secure healthcare systems with that mindset, see our founder’s podcast on
how to build HIPAA-compliant healthcare software.
It reinforces an important point from this article: successful healthcare platforms are not built by layering compliance on after the product works. They are built by making security, architecture, and trust part of the product from the start.
How Technology Rivers Approaches Healthcare Data Aggregation Products
Health data aggregation projects usually fail when teams treat interoperability, compliance, and product architecture as separate workstreams. Technology Rivers’ approach is stronger when those decisions are handled together from the start. That matters for aggregation apps because the product is only as strong as its weakest layer, whether that is patient matching, source normalization, access control, auditability, or the user’s ability to trust what they see.
Technology Rivers is positioned specifically for healthcare software that has to work in regulated environments, with experience across HIPAA-focused development, EHR and EMR integrations, secure cloud systems, and healthcare product delivery. That makes this kind of partner especially relevant for teams building aggregation apps that need to connect fragmented data without creating new compliance or reliability risks.
A practical advantage here is the company’s emphasis on compliance as an engineering decision, not just a legal checkbox. That is the right mindset for a health data aggregator app, where role-based access, audit logs, secure APIs, PHI handling, and long-term maintainability need to be built into the platform from day one. A useful related resource is how to ensure your healthcare software is HIPAA compliant in 2026, especially for founders validating whether their current architecture can actually support enterprise healthcare requirements.
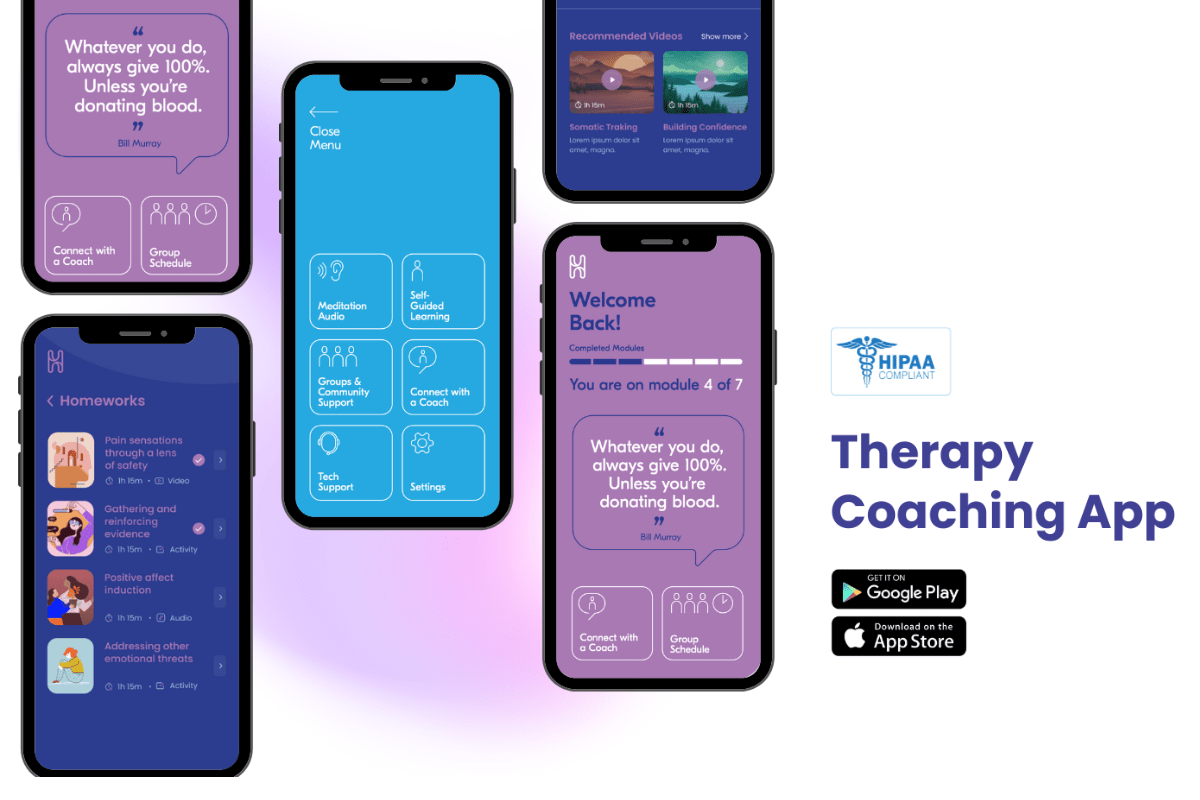
Technology Rivers also brings useful product breadth for this topic. Their healthcare work spans areas like remote patient monitoring, AI-assisted clinical workflows, patient-facing platforms, and other secure digital health systems. That matters because aggregation products rarely live in isolation. They often sit inside broader healthcare ecosystems that include provider workflows, device data, clinical documentation, scheduling, or patient engagement features.
One especially relevant example is a therapy coaching platform built around highly sensitive user data. In that product, privacy, trust, and secure architecture were essential from the beginning. That kind of experience translates well to health data aggregation, where user confidence depends on strong controls, thoughtful UX, and careful handling of sensitive records across multiple sources.
For teams thinking beyond initial MVP architecture, it also helps to learn from implementation-minded content rather than generic thought leadership. Resources like why most EHR integration projects fail and how to get them back on track and how to integrate your healthcare app with Epic EHR
are more directly useful for aggregation planning because they reflect the realities of source variability, integration planning, and long-term operational complexity.
If you are evaluating how to build a health data aggregator app, or trying to rescue an interoperability project that is already getting messy, speak with a healthcare software expert about the architecture, compliance, and integration choices that will shape the product long after launch.
Frequently Asked Questions
What does a health data aggregator app do?
A health data aggregator app pulls health information from multiple sources, such as EHRs, labs, pharmacies, payer platforms, and wearable devices, then organizes that data into one usable view. The goal is to reduce fragmentation and make healthcare information easier to access, understand, and act on across systems.
Is a health data aggregator app required to be HIPAA compliant?
If the app creates, receives, stores, or transmits protected health information on behalf of a covered entity or business associate, HIPAA requirements will usually apply. That means the platform needs appropriate safeguards for access control, auditability, encryption, and PHI handling, not just basic login protection.
What is the difference between a FHIR app and a health data aggregator app?
A FHIR app uses the FHIR standard to access or exchange healthcare data. A health data aggregator app may use FHIR, but its purpose is broader. It combines information from multiple sources, normalizes it, reconciles inconsistencies, and presents it in a unified workflow or interface.
How do you connect a healthcare app to multiple EHR systems?
Most teams use a mix of FHIR APIs, SMART on FHIR authorization, HL7 interfaces, and source-specific integration methods. The right approach depends on the systems involved, the workflow being supported, and how much consistency exists across source implementations. That is why EHR integration planning usually matters as much as coding.
What are the biggest risks in healthcare data aggregation?
The biggest risks include inaccurate patient matching, incomplete or stale records, source inconsistency, weak consent tracking, and poor HIPAA security controls. A product can technically aggregate data and still fail if users cannot trust where the data came from, how current it is, or whether access is properly governed.
How long does it take to build a health data aggregator app?
The timeline depends on the number of data sources, integration methods, security requirements, and workflow complexity. A narrow MVP focused on one high-value use case can move much faster than a broad platform connecting many systems. In most cases, scoping and architecture decisions have a major impact on delivery speed.